Understanding the “Too Many Requests” Phenomenon in the Digital Age
The seemingly simple message “Too Many Requests” might appear to be nothing more than a technical hiccup—a brief, out-of-the-blue error encountered during regular digital interactions. However, this message encapsulates a host of legal, technical, and ethical considerations that invite us to take a closer look at how internet infrastructure, digital law, and user rights intersect. In today’s discussion, we will dive in to explore how a message like “Too Many Requests” reflects not only a technical limitation but also poses important questions about digital regulation, accountability, and the balance of power between service providers and users.
Often accompanied by additional details such as a client IP address and a unique request identifier (for example, client_ip: 88.198.184.120 and request_id: 21949266307), this error message is more than just a system response—it is a signpost indicating that systems are working to manage traffic and protect resources. In this opinion editorial, we will dig into the legal framework behind such error messages, examine the implications of online traffic regulation, and consider what it means for our digital rights and freedoms. As we get into these issues, we will also outline some of the tricky parts and tangled issues that both lawmakers and technologists alike must address in today’s fast-paced digital environment.
Legal Frameworks Governing Digital Interactions
One of the key debates in modern internet law centers around how digital interactions should be regulated. The appearance of a “Too Many Requests” error is a reminder that online environments are managed by algorithms and automated systems that impose limits on user activity. These measures are critical to ensuring that the online ecosystem remains stable and secure. However, they also raise critical legal questions about fairness, access, and contractual obligations between service providers and users.
Regulating Internet Use: Balancing Stability and User Rights
Digital service providers, such as websites and online platforms, routinely enact rate-limiting measures to prevent overloading their servers. While these technical measures are designed to protect infrastructure by preventing automated abuse or unintended traffic spikes, they also intersect with the legal obligations that platforms have towards their users. Among the primary legal considerations are:
- Contractual Terms: Most online platforms include user agreements that stipulate the conditions under which their services are used. These contracts frequently empower service providers to limit requests when necessary for system health.
- Data Protection Laws: Such measures often involve tracking user activity, including IP addresses. This fact raises important questions regarding privacy and compliance with data protection regulations.
- Consumer Rights: Given that rate limiting can unintentionally restrict lawful access to content or services, users may be entitled to some legal recourse or, at the very least, transparent communication regarding these limits.
These legal areas are intertwined with the technical underpinnings of rate limiting, as providers must balance the efficient management of resources with respect for individual rights and contractual obligations.
Technical Mechanisms Behind “Too Many Requests”
The technical explanation for a “Too Many Requests” error is straightforward enough: servers use algorithms to monitor and control traffic penetration. When a client sends an excessive number of requests in a short period—whether intentionally or unintentionally—the server triggers a rate limit, temporarily halting further requests and returning the error message. However, when we get into the nitty-gritty of these mechanisms, we find a host of tangled issues that influence both the operational reliability of online services and their legal ramifications.
How Automated Systems Protect Infrastructure
In order to prevent potential attacks, abuse, or simply to manage load during peak times, digital service providers implement systems that automatically detect and restrict high-frequency requests. Some of the key elements in this process include:
- Traffic Analysis: Servers continuously monitor incoming traffic to identify abnormal patterns that could indicate malicious activity.
- Threshold Setting: Developers set thresholds for the number of requests allowed within a given timeframe to maintain infrastructure stability.
- Logging and Traceability: Unique identifiers, such as request IDs and IP addresses, are logged. This not only helps in troubleshooting but also in ensuring accountability.
In effect, these systems work as a form of digital triage by making rapid decisions about which requests to serve and which ones to delay or deny. While these measures are essential in protecting digital assets, the decision-making process is not without its twists and turns, as service providers must figure a path that is both technically sound and legally compliant.
Legal Implications of Data Collection and Client Identification
One of the distinguishing technical details on a “Too Many Requests” message is the inclusion of client-specific information, such as the IP address. Using client IP addresses for rate limiting ensures that system protection measures are both targeted and effective. However, this practice also raises important legal questions concerning privacy, data protection, and transparency.
Balancing Privacy with Accountability
Collecting and logging client IP addresses is standard practice, but it is not without controversy. The practices involved in data collection are:
- Data Minimization: Absolute retention of an IP address, along with a unique request identifier, must be justified on the basis that only a limited amount of data is needed to manage traffic efficiently. This concept is critical to data protection laws.
- Transparency: Users have a right to know what data is being collected and how it is used. Online platforms should provide clear, accessible information about their rate-limiting policies in their privacy policies or terms of service.
- Legal Accountability: In instances where data collection might cross into the realm of surveillance, legal oversight becomes super important. Governments and regulatory bodies may have input on whether these practices align with legal expectations regarding privacy.
In an age where privacy is a hot subject, the way service providers collect and store data associated with a “Too Many Requests” error is one of the finer shades of online regulation. Legal professionals are called to figure a path that ensures both the protection of digital infrastructure and the safeguarding of individual rights.
Contractual Obligations and User Expectations in a Digital World
The emergence of an error message like “Too Many Requests” compels us to reexamine the contractual relationships between online service providers and their users. Many platforms today rely on acceptable use policies (AUPs) and terms of use agreements that provide the legal framework for limiting user activities. These documents often include detailed provisions regarding behavior that is considered abusive or harmful to overall system performance.
Key Legal Concepts in Online Contractual Agreements
Several key legal elements come to light when we poke around the contractual side of rate limiting. These include:
- Consent: By using an online service, users are generally deemed to have consented to abide by its policies—including any measures that restrict excessive traffic.
- Enforceability: Courts have frequently upheld that platforms may lawfully enforce their rate-limit conditions as long as they are clear, reasonable, and communicated prior to any limitation taking effect.
- Remedies and Recourse: In cases where users feel they have been unfairly penalized by a rate limiting error, legal recourse may be pursued. This includes challenging the transparency and fairness of the restrictions imposed by the service provider.
It is worth noting that these aspects of contractual engagement can often be intimidating for the average user who may not be intimately familiar with legal jargon or the subtle details of online law. As such, greater clarity and simplicity in these agreements are essential so that all parties can steer through the legal landscape with confidence and mutual understanding.
Data Protection and Privacy: A Closer Look at Client IP Collection
When users receive a “Too Many Requests” message, they might not fully appreciate that behind the scenes, their digital footprint is being recorded. With information such as IP addresses being logged, a discussion about data protection and privacy is unavoidable. This issue is particularly loaded with tension in an era where digital privacy is increasingly under the spotlight.
Existing Privacy Protocols and Their Legal Basis
Data protection laws around the world share a common goal: to ensure that personal information is handled responsibly by organizations. Some of the fine points of these protocols include:
- Legitimate Interest: For many online platforms, collection of information such as IP addresses is justified as a means to ensure the safety and proper functioning of their systems.
- User Consent and Notification: Platforms are encouraged—or in some cases, legally required—to inform users about what type of data is being collected. This transparency is key to maintaining trust between providers and their users.
- Data Security: Beyond just collection, the ways in which data like IP addresses are stored and protected are critical factors in ensuring compliance with data security standards and regulations.
While regulations such as the General Data Protection Regulation (GDPR) in Europe or similar laws in other jurisdictions provide a legal backbone for these practices, there is still a need for constant monitoring of how these rules are implemented in everyday scenarios. The use of client IPs in error messages, while a technical necessity, also serves as a reminder that every piece of collected data must be managed with the utmost care, ensuring that legal boundaries are respected.
Fair Use and the Allocation of Digital Resources
At its core, the “Too Many Requests” error is a manifestation of the balance between fair resource usage and protecting a platform’s system integrity. Digital platforms must employ measures that are both effective from a technical perspective and aligned with equitable treatment of their users.
Evaluating the Balance Between Protection and Service
Rate limiting, while designed to prevent overload, inadvertently poses questions about fairness and accessibility. Several controversies arise from how these limits are set and enforced:
- Unintended Service Disruption: Even legitimate users, who are not engaging in harmful behavior, may sometimes trigger these limits unknowingly. This can result in temporary denial of service, which can be both overwhelming and off-putting.
- Scope of Usage: Determining the threshold for what constitutes “excessive” use is a delicate task that involves small distinctions and subtle details about user behavior. What is acceptable for one service might be too restrictive for another.
- Risk Management vs. User Experience: While it is super important to protect digital systems from abuse, companies must also remain aware of user frustrations and potential loss of goodwill.
For instance, online retailers, streaming services, or social media platforms all deploy their own versions of rate limiting. Each application has its own twisted blend of technical limits and legal guidelines, and understanding these differences is key to crafting policies that are perceived as both fair and effective. Ultimately, the challenge lies in finding a path that judiciously balances system security with the legal rights of users, ensuring that everyone receives a fair opportunity to access digital content and services.
Internet Regulation and the Role of Government Oversight
Rate limiting and the control of online traffic are not solely technical or contractual issues; they also raise broad questions about government oversight and digital regulation. As the internet continues to evolve, legal systems worldwide are challenged to keep pace with the changing digital environment. In many respects, the “Too Many Requests” error is a microcosm of the broader conversation surrounding regulation, accountability, and the balance of power between private entities and public interests.
How Legislation is Adapting to the Digital Reality
Government intervention in regulating online traffic has traditionally taken two forms: direct regulation of certain digital spaces and indirect oversight through consumer protection, privacy, and data security laws. Important areas to consider include:
- Antitrust and Fair Competition: Governments have a keen interest in ensuring that large digital platforms do not abuse their dominant positions. Rate limiting can sometimes serve as a tool to prevent competitors from flooding a market, but the use of such measures must be balanced against potential monopolistic practices.
- National Security: In light of recent global security challenges, many governments advocate for stringent monitoring of digital traffic to prevent cyber threats. However, increased surveillance must be carefully weighed against individual privacy rights.
- Public Accountability: Demands for transparency extend to the algorithms that enforce rate limiting. Lawmakers are calling for greater insight into how these automated systems make decisions—a call that is both reasonable and necessary in the age of AI and big data.
For digital law professionals and policymakers alike, working through these issues means tackling a number of complicated pieces with careful consideration of both public and private interests. The need for legislation that is both flexible and robust is clear, as the digital sphere continues to present nerve-racking challenges that require immediate legal responses without stifling technological innovation.
Case Studies: When Rate Limiting Meets the Courts
There have been several landmark cases where the enforcement of rate limiting and related data collection practices have come under judicial scrutiny. While not every instance of a “Too Many Requests” error leads to litigation, some have sparked significant debate about the balance between digital security measures and legal rights.
Examining Precedents in Digital Access and Liability
Let’s consider a few cases and scenarios that illustrate the multiple angles of this issue:
- The Unauthorized Blocking Case: In one matter, a prominent online retailer was challenged for blocking access to its services after a user triggered repeated rate limits. The court had to consider whether the blocking was a reasonable safeguard or an overreach that undermined the user’s right to access a digital service.
- Data Collection Disputes: Another case revolved around the extent to which an online platform could log IP addresses without explicit user consent. Here, the judge examined whether the collection and subsequent retention of data were reasonable steps for protecting system integrity or if they veered into invasive territory.
- Fair Use and Contractual Fairness: Disputes have also arisen over contractual terms that users might not fully understand, leading to claims of unfair practice. In these cases, the courts often had to weigh the written terms of service against the actual expectations of the average user.
Each of these cases underscores the need for clear and balanced policies. The courts serve as a reminder that while technical safeguards such as rate limiting are essential, they must also be accompanied by transparent legal frameworks that protect users from unreasonable exploitation.
Exploring the Broader Implications of Automated Enforcement
Beyond the immediate legal and technical concerns, the concept of automated enforcement raises questions about digital fairness, accountability, and the potential for bias in algorithmically driven decisions. The “Too Many Requests” error is simply one example of a broader trend in which machines make rapidly executed decisions that have significant real-world consequences.
Automated Decision-Making and Its Legal Shadows
Several key considerations emerge when we look at the intersection of automation and law:
- Accountability: When an algorithm denies access, it is often unclear who is responsible for that decision—the developer, the company, or the system itself? Legal systems must determine how to assign responsibility in cases where automated processes lead to an unfair or unintentional denial of service.
- Bias and Discrimination: While rate limiting is intended to be a neutral process, there is a risk that automated systems might inadvertently favor certain types of traffic over others, potentially leading to discriminatory outcomes. Addressing these slight differences and subtle details in algorithm design is a task that demands careful legal and technical oversight.
- Transparency in Algorithms: There is growing pressure on service providers to reveal the inner workings of their automated decision-making systems. Such transparency is essential in ensuring that limits are applied fairly and that users can understand and, if necessary, challenge automated decisions.
In grappling with these questions, legal practitioners are often called upon to review not only the technical design of these algorithms but also the legal standards that govern fairness and accountability in automated systems. Resolving these issues means working through multiple layers of potential conflict between public interest and private enterprise, ensuring that accountability is maintained without impeding technological advancement.
The Future of Digital Regulation and Rate Limiting
As digital interactions continue to expand and technology becomes even more integral to everyday life, the need for clear regulation of online behaviors is set to grow. The “Too Many Requests” error, although a seemingly small technical signal, stands as a bellwether for larger questions about how best to manage digital resources and safeguard individual rights in an increasingly online world.
Emerging Trends in Digital Oversight
Looking ahead, several emerging trends and key issues are likely to shape the future of digital regulation:
- Dynamic Policy Adjustment: With rapid advancements in artificial intelligence and machine learning, it is plausible that future rate limiting systems will be more adaptive, tailoring their responses based on real-time analysis of traffic patterns and user behavior. This dynamic approach may help reduce unnecessary blocks while still maintaining system integrity.
- Stronger Data Protection Measures: As public concern surrounding privacy intensifies, governments and regulatory bodies may update and strengthen data protection guidelines to ensure that all automated processes, including rate limiting, are aligned with users’ privacy rights. Service providers, in turn, will need to develop systems that are both efficient and in strict compliance with evolving legal standards.
- Enhanced User Communication: There is a growing call for greater transparency. Ensuring that users are well informed about why a particular action has been taken, such as triggering a “Too Many Requests” message, is essential to building trust. This includes more user-friendly explanations in service agreements and through direct communication channels during error instances.
- International Legal Harmonization: Given that digital platforms often operate across borders, achieving some degree of international coherence in digital regulation could be a super important goal. Standardizing aspects of rate limiting and data collection policies might help create a more predictable, fair digital environment for all users.
These trends indicate that in the face of ever-changing technological landscapes, a rigid approach is no longer sufficient. Instead, the legal frameworks governing online interactions must be flexible enough to allow for technological innovation while ensuring that users remain protected against any unfair practices or accidental overreach.
Lessons Learned: Policy Recommendations for a Balanced Digital Ecosystem
The ongoing dialogue around error messages like “Too Many Requests” offers an important opportunity to reflect on best practices in both technology management and legal regulation. Drawing from the discussions above, several recommendations emerge that can help create a fairer and more efficient digital ecosystem:
Practical Steps for Service Providers and Lawmakers
Below is a summary of key recommendations for service providers and lawmakers to consider:
| Recommendation | Details |
|---|---|
| Clear User Agreements | Establish transparent, easy-to-understand terms of use that clearly explain rate limiting and data collection practices. |
| Regular Policy Review | Update internal policies and technical thresholds periodically to stay aligned with evolving technology and legal standards. |
| Enhanced Customer Support | Provide better communication channels for users to understand and, if necessary, contest rate limiting decisions. |
| Data Protection Compliance | Routinely audit data handling practices to ensure compliance with local and international privacy laws. |
| Algorithmic Transparency | Offer insights into how automated systems function and how decisions are made, fostering trust and accountability. |
These recommendations are not exhaustive, but they provide a framework for approaching the myriad of twisting turns and confusing bits presented by the intersection of technology and law. Whether you are a legal professional, a technology developer, or a policymaker, taking decisive steps in these areas is critical for building a balanced digital future.
The Broader Context: Digital Rights and User Empowerment
Beyond technical and legal considerations, the enforcement of rate limiting touches on broader themes in today’s digital society. At its heart, these measures challenge us to think critically about user empowerment, fairness, and the balance of power in digital ecosystems. The ubiquity of messages like “Too Many Requests” forces us to ask: Who really controls the flow of digital information, and how can we ensure that power is wielded responsibly?
Empowering Users Through Transparency and Accountability
Individuals deserve to have a clear understanding of how digital tools operate, especially when automated decisions directly impact their access and experience. Here are several ways to further empower users:
- Enhanced Visibility:
- Clear explanations during rate limiting errors that describe why the error occurred and what steps might rectify the situation.
- Accessible documentation of the technical policies that underpin service restrictions, written in plain language.
- User Feedback Channels:
- Establish open lines of communication where users can report issues or appeal decisions regarding automated bans.
- Digital Literacy Initiatives:
- Support educational programs to help users understand the fine points of digital law and online rights, thereby reducing the intimidating aspects of technical error messages.
Providing users with the tools and knowledge to understand when and why their access is restricted not only builds trust between consumers and providers but also fosters a more informed public that is capable of engaging with the digital world on equitable terms.
Industry Perspectives: Bridging the Gap Between Technology and Law
Within the tech industry, there is an ongoing discussion regarding the need to bridge the gap between the fast-paced world of technological innovation and the slower, albeit essential, processes of legal regulation. The automatic nature of systems that generate messages like “Too Many Requests” means that decisions are often made with little human oversight—and this approach necessitates legal frameworks that can adapt to these rapid changes.
Collaborative Approaches to Policy Development
Some of the ideas currently floating around include:
- Joint Task Forces: Establishing collaborative groups that include legal experts, technologists, and consumer advocates to regularly review and update online conduct guidelines.
- Standardized Best Practices: Developing industry-wide standards for rate limiting and data protection that can be uniformly applied, regardless of jurisdiction.
- Regular Audits: Implementing third-party audits of automated systems to ensure that their operations align with both best practices and legal requirements.
Such collaborative efforts are poised to create an environment where technological innovation does not run counter to user rights. Instead, both realms can evolve together with an eye toward fairness and accountability, ensuring that systems like rate limiting serve their purpose without harming legitimate digital participation.
Conclusion: Charting a Path Forward in an Ever-Evolving Digital Landscape
The message “Too Many Requests,” though terse and technical, opens a window into the complex relationship between technology, law, and everyday digital interactions. As we have taken a closer look at the legal frameworks, technical safeguards, data protection concerns, and the broader policy implications, it becomes clear that these issues are full of problems but also offer opportunities. There is a tremendous need—and indeed, a responsibility—for service providers, lawmakers, and digital users to figure a path that ensures both security and fairness in an increasingly connected world.
By revisiting and rethinking the systems that give rise to automated decisions, whether through refined contractual terms, increased transparency in data collection, or a more balanced approach to enforcement, we can mitigate the nerve-racking impact of these errors. Rather than allowing automated systems to function as inscrutable black boxes, we have an opportunity to create digital ecosystems that respect both the infrastructure’s needs and the rights of every individual.
This editorial has attempted to poke around the multifaceted world of rate limiting—outlined its historical context, explored its legal and technical settings, and provided policy recommendations aimed at improving our digital future. As digital law continues to evolve, continuous dialogue among legal professionals, technologists, and the public remains essential. Only through such collaborative efforts can we ensure that the digital world remains a space where technology and human rights evolve in tandem, rather than at odds.
In the final analysis, every time a user encounters that small message saying “Too Many Requests,” it is a reminder of the intricate interplay of technology, privacy, legal rights, and corporate responsibility. The challenge moving forward is not merely to manage digital traffic, but to do so in a way that is fair, transparent, and built upon a foundation of trust and mutual respect. It is up to all stakeholders—developers, legal professionals, regulators, and users alike—to take the wheel, work through these challenging parts, and create a digital future where innovation and accountability go hand in hand.
Ultimately, while the error message “Too Many Requests” might seem like a minor inconvenience in the grand scheme of digital operations, it encapsulates some of the most pressing concerns facing our interconnected world today. As we strive to find your way through technological change, trust that each step taken toward clearer, fairer digital policies will help ensure that the internet remains a space that not only pushes the boundaries of innovation but also protects the rights of those who rely on it the most.
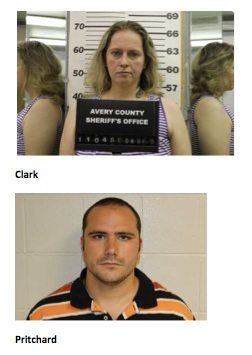
Originally Post From https://www.averyjournal.com/arrests_land/avery-county-arrest-report/article_72102642-c383-424e-a8b0-47d6cdfafbb1.html
Read more about this topic at
What is the deal with “Rate Limit Exceeded” on twitter?
Twitter Rate Limit Exceeded | 6 Instant Fixes